Dude, by default they intercept all customers' DNS queries and redirect them to their DNS servers. Then, they answer the DNS queries with their servers and spoof the originating server within the DNS response to make it look like they didn't intercept it. They're a regular man-in-the-middle! Total lameness.
Now, normally this wouldn't bother me too much because I would prefer to use an ISP's DNS servers. They will typically be your fastest resource for a DNS response. But spoofing responses to me? That's over the top. What if I wanna use OpenDNS to filter my internet? Or what if I just simply wanna troubleshoot a DNS issue by querying another ISP's DNS server? No go.
I know why they do this. They are trying to control bandwidth on their end. But this is a little extreme.
There's another side to this: My ISP's DNS servers stink!! They go down for 10 minutes at a time without warning. During these periodic outages I can ping by IP address but not by name and the internet is effectively dead. Total lameness.
So…We have DNS servers that aren't reliable and we have an ISP that forces you to use the bad DNS servers. Great situation!
After fighting with my ISP's customer service and getting nowhere, I decided it was time to take matters into my own hands and solve this problem myself.
First, I proved this was indeed the problem by setting my WZR-HP-G300NH2/Gargoyle (see previous post) router to use Google's DNS servers and then checking the logs. The logs showed that I was actually talking to my ISP's DNS servers even when I made queries to Google!
I started thinking…They've got to be intercepting this based on port number…What if there was a DNS server out there somewhere that actually listened on an alternate port? Lo, and behold there is! OpenDNS' servers listen on both 53 and 5353! Now all I needed to do was make make Gargoyle/OpenWRT talk to their servers on the alternate port, thus circumventing my ISP's DNS servers!
Using a wiki designed for setting up DNSCrypt on OpenWRT (which maybe I will setup sometime), I SSHed to the router and backed up /etc/config/dhcp and then edited it using vi (I also backed up my config from the web interface):
cp /etc/config/dhcp /etc/config/dhcp.bak
vi /etc/config/dhcp
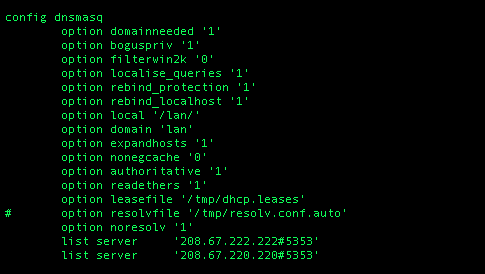
If you don't know how to use vi, check here. As shown below, under the "config dnsmasq" section I then commented the "option resolvfile" line and added 3 more lines under that line:
option noresolv '1'
list server '208.67.222.222#5353'
list server '208.67.220.220#5353'
(Make sure you match the formatting/spacing shown in the image.)
As you can see, the last 2 lines tell the router to use OpenDNS' servers and talk to them on alternate port 5353. Then I created an OpenDNS account (not necessary) and restarted the router's DNS daemon:
/etc/init.d/dnsmasq restart
...Now OpenDNS has a page at http://internetbadguys.com that they block just for testing purposes...so I went to a computer to see if I was successfully blocked (I cleared the DNS cache on the computer first):
Good! Here's what would have showed had I not been successfully blocked by OpenDNS' filtering:
I also checked my router logs and found lots of entries with 208.67.222.222:5353:
Very good!! I searched my logs further for any queries to my ISP's DNS server and found none! I then backed up my router config, flushed the DNS cache on my boxes and laughed all the way home:
Windows: ipconfig/flushdns
Mac OS X ML: sudo killall -HUP mDNSResponder
Recap:
My ISP = fail
My ISP = pwned
Me = Happy!



On backfire gargoyle dont work !
ReplyDeleteAny suggestion ? thanks.
Jm
Portugal
I would head to the Gargoyle forums if I were you. They should be able to help you. Sounds like maybe you are trying to install Gargoyle on top of OpenWRT instead of just using a Gargoyle image?
ReplyDeleteI just use gargoyle image version stable 1.4.7. On fonera 2200.
DeleteJM
Portugal
Try here: http://www.gargoyle-router.com/phpbb/index.php
DeleteYou only edit the /etc/config/dhcp ?? comment the resolv.conf.auto and add the 2 lines ?
DeleteNo, there are 3 lines there. Sorry if it isn't super-clear from my post. Although I did say "3 more lines". Maybe I will edit it.
DeleteAnyhow, I am suspecting that you have omitted this line, which is shown in the image in the post:
option noresolv '1'
*edited post
ReplyDeleteI am using DLink wireless router...can you please tell me how can I bypass my ISP's DNS because I cannot access neobux through my local DNS. Any help would be appreciated.
ReplyDeleteWhat troubleshooting steps have you done to confirm this is actually a DNS issue and not something else? Google a bit on OpenWRT and see if your router is compatible.
ReplyDelete